Building a Safer Digital World
Security is no longer optional. In a world powered by digital transformation, cloud computing, and remote work, both individuals and organizations face growing risks. Cyberattacks, data breaches, and identity theft have become common headlines. Whether you manage a business or simply browse online, understanding security fundamentals is essential to protecting your data, finances, and reputation.
Understanding Modern Security Threats
The Rise of Cybercrime
Cybercrime has evolved from isolated hacking attempts to organized, large-scale operations. Attackers now use sophisticated methods such as ransomware, phishing, and social engineering to exploit vulnerabilities. These threats target not only large corporations but also small businesses and individuals.
Ransomware can lock critical systems until a payment is made, while phishing emails trick users into revealing sensitive information. Even a single weak password can open the door to serious consequences.
Human Error: The Weakest Link
While technology plays a significant role in security, human behavior remains one of the biggest vulnerabilities. Clicking unknown links, reusing passwords, or ignoring software updates can expose systems to threats. Security awareness and proper training are often the first and most effective line of defense.
Key Elements of Strong Security
Proactive Protection
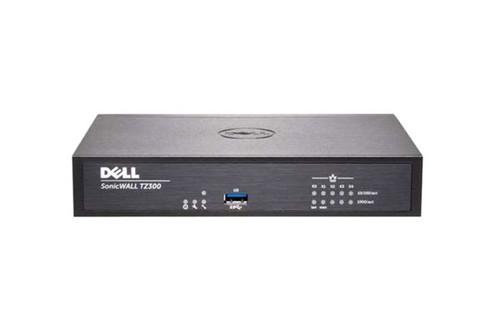
Strong security begins with proactive measures. Regular software updates, multi-factor authentication, encrypted communications, and secure network configurations help prevent unauthorized access. Firewalls and endpoint protection tools add additional layers of defense.
Organizations should also implement regular security audits and vulnerability assessments to identify weaknesses before attackers do.
Data Protection and Backup
Data is one of the most valuable assets in the digital age. Protecting it requires encryption, secure storage solutions, and consistent backup strategies. In the event of a breach or system failure, reliable backups ensure business continuity and minimize downtime.
For businesses handling customer information, compliance with data protection regulations is not only a legal requirement but also a trust-building measure.
Creating a Culture of Security
Awareness and Responsibility
Security is not just an IT department’s responsibility. It is a shared commitment across an organization. Employees should understand best practices, recognize suspicious activity, and feel empowered to report concerns.
Leaders play a crucial role by prioritizing cybersecurity investments and fostering a culture that values data protection.
Conclusion: Security as an Ongoing Commitment
Security is not a one-time setup but a continuous process. As technology evolves, so do the threats. Staying informed, implementing strong protective measures, and promoting awareness are essential steps toward building a safer digital environment. By taking security seriously today, we protect not only our systems but also our future.
- Arte
- Causas
- Artesanía
- Bailar
- Bebidas
- Película
- Fitness
- Alimento
- Juegos
- Jardinería
- Salud
- Hogar
- Literatura
- Musica
- Redes
- Otro
- Fiesta
- Religión
- Compras
- Deportes
- Teatro
- Bienestar